We Are Constantly Reminded To Create Complex Passwords And Change Them Often.
But the better the password, the harder it is to remember. So what do many of us do? We settle for a simple word or sequence of numbers. Or, if we do create a clever password, we write it down near our computer. Maybe it’s so “good,” we use it on multiple accounts.
Why Should We Care About Strong Passwords?
Personal data is regularly stolen from companies and not just small companies with lax security. Attackers have successfully gotten data from companies like SONY, Adobe, Facebook, and LinkedIn – companies that manage account information for thousands or millions of people. The username (often an email address) and password pair is the lock you put on your personal information. Once an email address is found and public, it’s only a matter of guessing the password.
Your email address may already be known to hackers. You can explore the collections of known email addresses with sites like: HaveIBeenPwned.com
Your Password May Already Be For Sale On Hacking Forums.
Sadly, you can’t control how a company treats the data you hand over. And, with each breach, the collection of stolen accounts creates a useful database against which to crack newly stolen names and passwords. Unfortunately, lists of stolen passwords can be bought and sold for years before they come to light. Imagine how much more vulnerable you are if you reuse that password.
The Good News: There Are A Couple Of Reliable Approaches To Creating Secure, Strong Passwords.
- Practice techniques to create passwords that are hard to crack yet easy to remember and,
- Use a password management tool with good reputations.
Finally, the security landscape changes all the time. Great advice one year, when discovered by hackers, could become bad advice the next. Yearly improvements in technology help hackers as well – for example, quantum computers might make light work of cracking that trillion-year password – or not.
At the very least, prioritize your efforts. For websites or apps that access financial accounts or other sensitive data – you need strong passwords that you don’t use anywhere else. Fix that now!
Design A Strong Password That Is Hard To Crack But Easy To Remember – 4 Steps
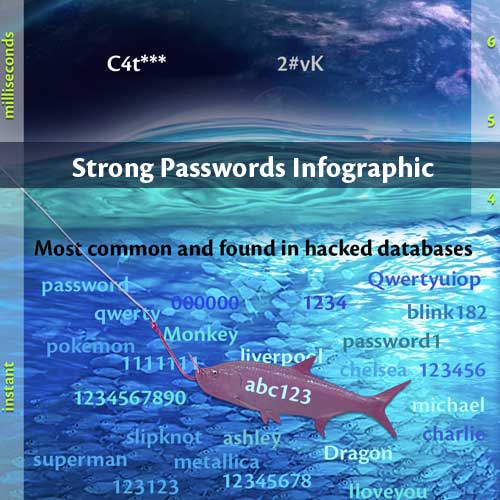
1) Don’t Use Common Passwords That Attackers Have Already Discovered Or Are Common: If Any Of Your Passwords Are In Top 20 Common Passwords Of 2019 List Change Them Now!!
- 123456789
- qwerty
- password
- 1111111
- 12345678
- abc123
- 1234567
- password1
- 1234567890
- 123123
- 000000
- Iloveyou
- 1234
- 1q2w3e4r5t
- Quertyuiop
- 123
- Monkey
- Dragon
Here’s a fun list of the top 100 worst passwords from 2019
Why? Hackers search for these common passwords first, and that nets them a lot of fish.
2) Avoid Single Words That Can Be Found In A Dictionary In Your Language.
Example: Labrador, underwear
Why? It’s not hard or time-consuming to compare your password to an entire list of dictionary entries.
3) Mix Uppercase, Lowercase, Numbers, Symbols. Doing This Increases The “Search Space Depth.”
Example: in an eight-character password here’s how long it takes to figure out a password with an offline, fast attack (100billion guesses per second): lowercase only: abcdefgh = 2.17 seconds,
add uppercase: Abcdefgh = 9.08 minutes,
add a symbol: Abcedfg! = 7.66 hours,
add a number: Abcdef8! = 18.62 hours.
Why? When you increase the “search space depth,” you increase the amount of time/effort required to hack. The search depth of Abcdef8! is 26 + 26 + 10 + 33 = 95. The search space length = 8. The count of all possible passwords with this alphabet size and up to this password’s length = 6,704,780,954,517,120.
4) Length Is As Or More Critical Than Entropy (A Bazaar Mix Of Letters And Symbols That You’ll Never Remember).
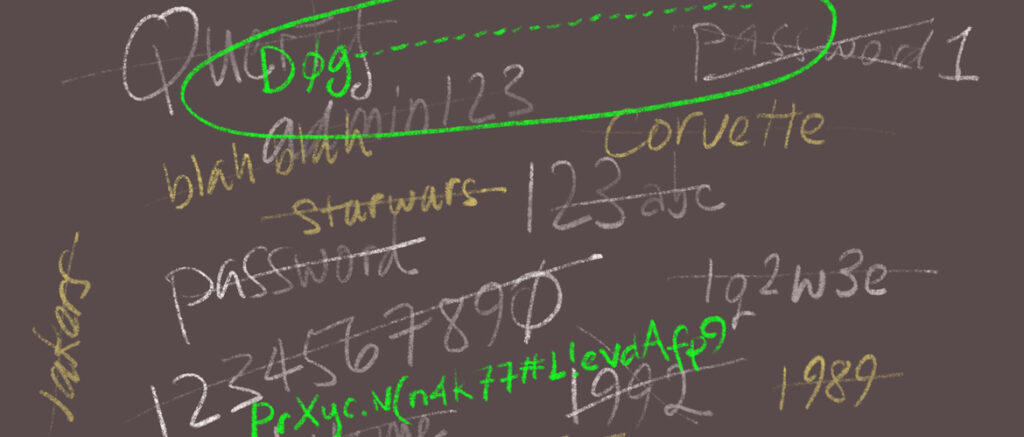
Strong password example: C4t——————— would take 95 times longer to crack than PrXyc.N(n4k77#L!eVdAfp9
Why? The first password is simply one character longer (24 total characters) than the second. The attacker succeeds only with an exact match. Both examples are using the mixed uppercase, lowercase, number, special symbol, but the first is one character longer, which increases the amount of time:
C4t——————— = 9.38 hundred billion trillion centuries
PrXyc.N(n4k77#L!eVdAfp9 = 9.88 billion trillion centuries
So, both passwords above are great, but you will remember the first: Cat substituting 4 for the “a” followed by 21 dashes.
TAKE AWAY: Password Length Matters Most, Mixed Characters Help.
Use a full character depth (upper, lower, number, symbol) to create a word or sentence you’ll remember – then make it long – pad it with symbols or some pattern unique to you.
Example: +++++My+++++5+++++Cats+++++
This quick video sums it all up:
Use A Decent Password Manager Application
The best method is to create strong passwords (as above), use them only once, and remember them. If you’re unlikely to do this, a password management tool is next best.
For this option to be useful, you want the ability to sync across all of your devices. You still need to create or let the tool generate complex long passwords unique to each account. The advantage here is you only have to remember the password to the Password Manager. So make that a good one.
At our company, we often use 1Password or KeePass, but the following reviews at the end may help you vet out a password manager that makes sense for your situation.
CONCLUSION
- Passwords are a necessary evil.
- Your favorite passwords may already be in a hacker’s database.
- Use a strategy that works best for you. Create long, unique strong passwords that you remember.
- Deploy a secure password management application to manage your complex passwords.
- At a minimum, prioritize passwords that are gateways to important information about you and only use them once.
- Check regularly for password best practices.
- Spot check your passwords with password checkers. Checkers may be inconsistent but the effort to check at all will lead to stronger passwords.
- If you are responsible for designing and implementing a password policy for your enterprise; in addition to the advice above, reach out to experts. A good password plan is supported by a formal password policy and infrastructure designed for security.
INTERESTING READING About Passwords – Creating, Evaluating And Managing:
Password related:
How Big is Your Haystack Lets you experiment with different passwords and estimate the time it takes to guess them.
From Troy Hunt: Here’s Why [Insert Thing Here] Is Not a Password Killer. Why passwords are probably here to stay.
A deep-dive discussion of Password Managers from Bruce Schneier on Security.
Here’s another tool to help you create or fine-tune existing passwords to make them stronger: https://www.safetydetectives.com/password-meter/
2020 Reviews of Password Managers:
From cnet.com: The Best Password Managers of 2020 and How to Use Them
From Digital Trends: Best Password Managers
And beyond:
Musings on Quantum computing: Scott’s Supreme Quantum Supremacy FAQ!
Readers have requested more resources for privacy protection:
Reviews of Identity Theft Protection services, from Money.com: https://money.com/best-identity-theft-protection/